Please wait.
Article
How different is security across industries?
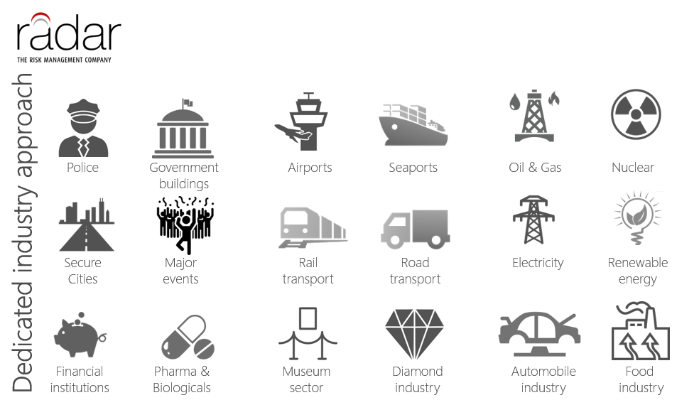
The risk context is specific for any industry or sector, but; the risk management system dealing with risks is exactly the same. The ISO31K Risk Management Standard is a good proof: the standard can be applied to any industry, private or public.
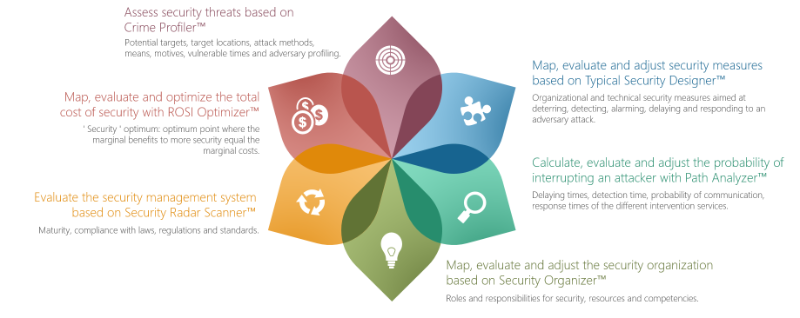
In my former post, I presented Securifyer™: a total and integrated security risk management system developed by a global network of risk management experts. The 6 interlinked modules of the security management system can be applied to any industry, public or private.
Crime Profiler™ identifies security risk scenarios, specific for the industry based on the internal and external context. The key element in this context are the objectives of the organization. Risk is the effect of uncertainty on objectives (ISO31K). The top 5 risk scenarios for an airport are not the same as the top 5 risk scenarios for an energy facility, a public transport organization or a financial institution, but the thought process on identifying, analyzing and evaluating security risks is the same.
Security measures differ from industry to industry, but across all industries: their objectives are the same: deter, detect, alarm, delay, respond and recover. We developed Typical Security Designer™ to develop security measures to mitigate the security risk scenarios identified by Crime Profiler™ in the most effective way.
Independent of any industry, the key question is: what is, given the current security, the probability that an adversary is interrupted, before the event has negative consequences on our objectives? Path Analyzer™ calculates, evaluates and gives you the opportunity this probability of interruption, based on the data of Crime Profiler™ and Typical Security Designer™.
A state-of-the-art security management system is only possible with a state-of-the-art security organization with clear roles and responsibilities, adequate resources and competences. The Security Organizer™ module supports in mapping, evaluating and adjusting the security organization.
As any quality management system, security is a continuous cycle of planning, implementing, monitoring and reviewing for continuous improvement. To support this process, the Radar Network developed Security Radar Scanner™ to measure the maturity of the security risk management process and compliance with laws, regulations and standards.
Last but no least: why should any organization invest in security? Any security professional not able to make the ‘security business case’ should not waste anybody’s time and do some homework first. Five key questions to prepare for any industry with ROSI Optimizer™:
- What is the current cost of security?
- What is the composition in terms of Capex, Opex and type of security measures?
- What is the % of security in terms of total costs?
- What is the % of security in terms of revenues (protected)?
- What are KPI’s related to Return On Security Investment?